Моя wifi карточка:
keiz@ekz:/opt/wifi/air$ lspci -v
04:06.0 Network controller: RaLink RT2561/RT61 rev B 802.11g
Subsystem: D-Link System Inc AirPlus G DWL-G510 Wireless Network Adapter (Rev.C)
Flags: bus master, slow devsel, latency 32, IRQ 20
Memory at fddf0000 (32-bit, non-prefetchable) [size=32K]
Capabilities: <access denied>
Kernel driver in use: rt61pci
Kernel modules: rt61pci
keiz@ekz:/opt/wifi/air$ lsmod | grep rt61pci
rt61pci 21957 0
rt2x00pci 6993 1 rt61pci
rt2x00lib 31575 2 rt61pci,rt2x00pci
eeprom_93cx6 1789 1 rt61pci
crc_itu_t 1739 2 rt61pci,firewire_core
Устанавливаем пакет kismet в систему:
keiz@ekz:~$ sudo aptitude install kismet
Теперь нужно настроить конфигурационный файл:
Но сперва создадим резервную копию:
keiz@ekz:~$ sudo cp /etc/kismet/kismet.conf /etc/kismet/kismet_10062012.conf
Редактируем:
keiz@ekz:~$ sudo nano /etc/kismet/kismet.conf
keiz@ekz:~$ sudo kismet -c rt61,wlan0,ralink
source=rt61,wlan0,wireless
Правка конфигурационного файла завершена, переведем нашу wifi карточку в режим мониторинга:
keiz@ekz:~$ sudo ifconfig wlan0 down
keiz@ekz:~$ sudo iwconfig wlan0 mode monitor
Запускаем приложение kismet:
keiz@ekz:~$ sudo kismet
Launching kismet_server: //usr/bin/kismet_server
Suid priv-dropping disabled. This may not be secure.
No specific sources given to be enabled, all will be enabled.
Non-RFMon VAPs will be destroyed on multi-vap interfaces (ie, madwifi-ng)
Enabling channel hopping.
Enabling channel splitting.
NOTICE: Disabling channel hopping, no enabled sources are able to change channel.
Source 0 (wireless): Enabling monitor mode for rt61 source interface wlan0 channel 6…
Source 0 (wireless): Opening rt61 source interface wlan0…
Will attempt to put networkmanager to sleep…
Allowing clients to fetch WEP keys.
WARNING: Disabling GPS logging.
Logging networks to /var/log/kismet/Kismet-Jun-10-2012-2.network
Logging networks in CSV format to /var/log/kismet/Kismet-Jun-10-2012-2.csv
Logging networks in XML format to /var/log/kismet/Kismet-Jun-10-2012-2.xml
Logging cryptographically weak packets to /var/log/kismet/Kismet-Jun-10-2012-2.weak
Logging cisco product information to /var/log/kismet/Kismet-Jun-10-2012-2.cisco
Logging data to /var/log/kismet/Kismet-Jun-10-2012-2.dump
Writing data files to disk every 300 seconds.
Mangling encrypted and fuzzy data packets.
Tracking probe responses and associating probe networks.
Reading AP manufacturer data and defaults from //etc/kismet/ap_manuf
Reading client manufacturer data and defaults from //etc/kismet/client_manuf
Using network-classifier based data encryption detection
Not tracking duplicate IVs
Putting networkmanager to sleep…
Dump file format: wiretap (local code) dump
Crypt file format: airsnort (weak packet) dump
Kismet 2008.05.R1 (Kismet)
Logging data networks CSV XML weak cisco
Listening on port 2501.
Allowing connections from 127.0.0.1/255.255.255.255
Registering builtin client/server protocols…
Registering requested alerts…
Registering builtin timer events…
Gathering packets…
Launched client, pid 3624
Launching kismet_client: //usr/bin/kismet_client
Looking for startup info from localhost:2501…… found.
Connected to Kismet server 2008.05.R1 on localhost:2501
Reading AP manufacturer data and defaults from //etc/kismet/ap_manuf
Reading client manufacturer data and defaults from //etc/kismet/client_manuf
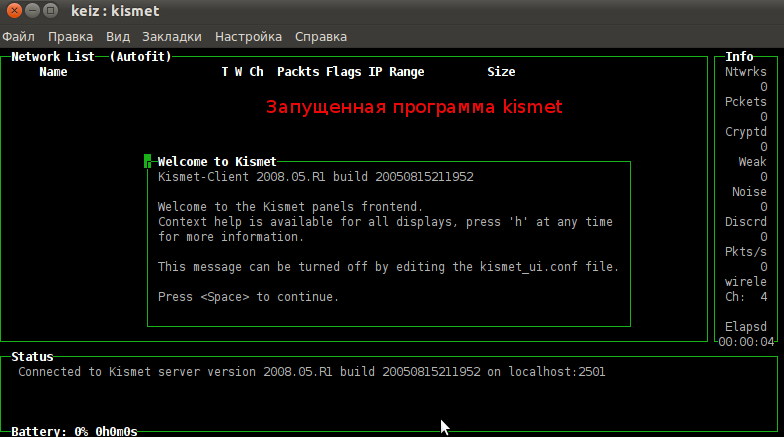
Оно запущенной и работающей программы:
Чтобы вернуть сетевую карточку в рабочий режим:
keiz@ekz:~$ sudo iwconfig wlan0 mode managed